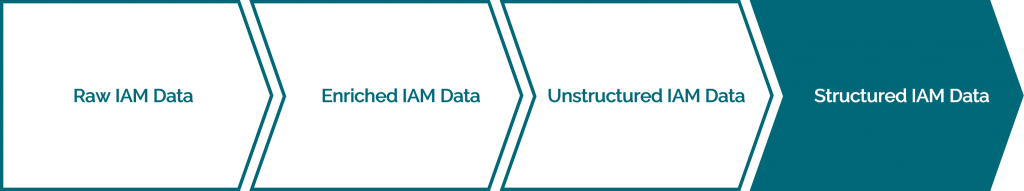
Structuring data
Identity and Access Management data are events related to users and roles lifecycles:
- User failed authentication
- User successful authentication
- User departures
- User arrivals
- User password changes/reset
- New authorization obtained
- New role assignment
- ...


The solution collects and sort data in order to make it actionable by users when consulting and creating views and dashboards.
Business-oriented views of IAM events (users arrival/departures, password changes, user authentications successes/failures, etc) are made available to the end user.
<<Back to Product Features
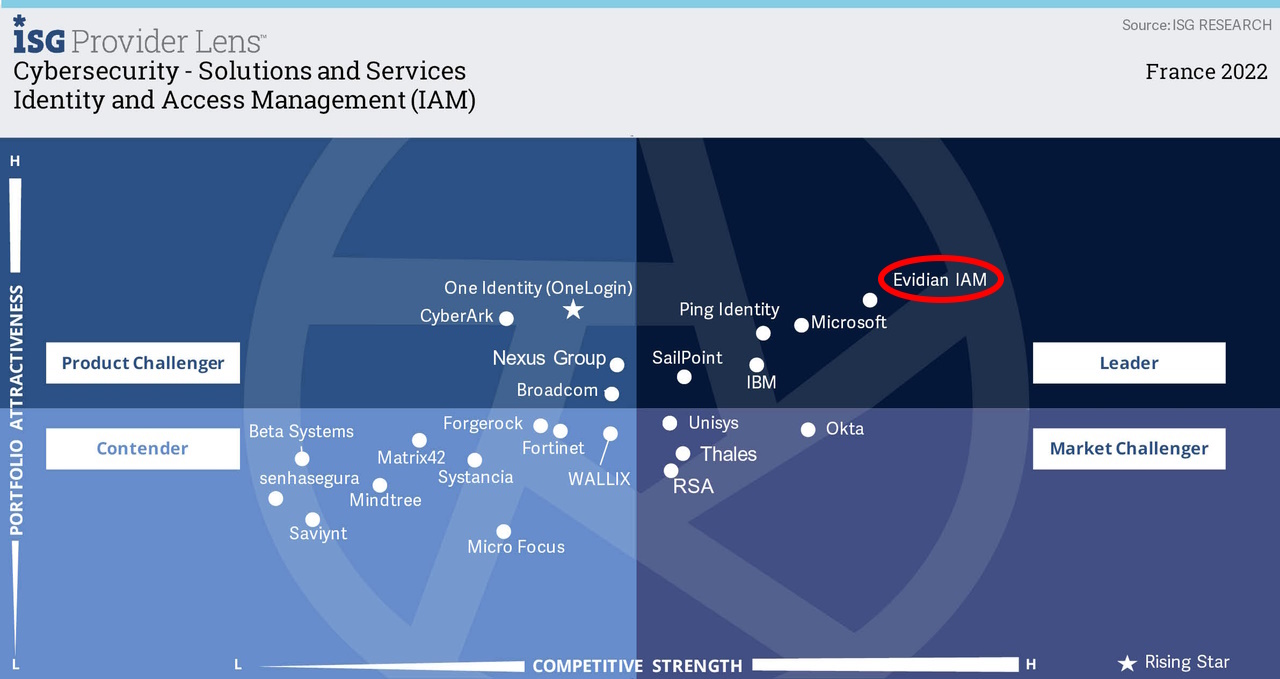
Orbion
Evidian takes care of everything related to your Identity and Access Management with Orbion (Identity as a Service)
Learn more >
Identity Governance and Administration
Manage access and authorization of all your users in your company
Learn more >
Web Access Manager
Gateway for web apps with SSO, multi-factor authentication, identity federation
Learn more >
Authentication Manager
Authentication Manager
Enterprise multi-factor & passwordless authentication on Windows PCs
Learn more >
Enterprise Single Sign-On (SSO)
Secure access to legacy and web apps on PCs & mobiles with SSO